Why Application Whitelisting is a Game Changer for Cybersecurity
In today’s cybersecurity landscape, businesses are constantly bombarded with new threats. Cybercriminals use everything from phishing emails to malicious scripts to breach systems and steal...
What happens when a ransomware group targets your business?
The Growing Threat of Ransomware: How Businesses Can Protect Themselves Cybercriminals are more sophisticated than ever, and ransomware groups are becoming highly specialized in their attacks. These...
Astaroth Phishing Kit – More Dangerous Than EvilGinx?
The Rise of Reverse Proxy Attacks: How Hackers Bypass Multi-Factor Authentication? In the ever-evolving world of cybersecurity, a new phishing threat has emerged, making it easier for hackers to...
Why You Should Always Audit Your Credit Card Statements
Most people check their bank accounts for large, unusual transactions, but smaller details often go unnoticed. A recent experience reminded me why reviewing every charge is so important. The...
How to Lock Down Office 365 on a Per-Device Basis Using Conditional Access Policies
Ensuring the security of Office 365 is critical, especially in a world where cyber threats are constantly evolving. While multi-factor authentication (MFA) and strong passwords add layers of...
Understanding Evilginx Reverse Proxy Attacks and How to Protect Your Business
Cybercriminals are constantly evolving their methods, and one particularly dangerous attack vector that has been compromising business emails—even those protected by multi-factor authentication...
Triple Extortion Ransomware
Triple Extortion: The Next Level of Cyber ThreatsRansomware attacks are getting more aggressive—and now, hackers have taken extortion to a whole new level.🔹 Step 1: They breach your network and...
What happens when you get locked out of your icloud account?
I was on a phone call yesterday with someone who had her iCloud account hacked over the weekend and her cell phone number stolen. We are not sure exactly how the hackers were able to gain access to...
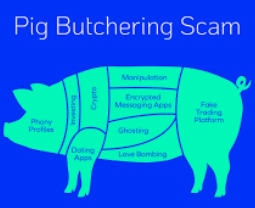
Unmasking the Pig Butchering Scam: How to Spot and Avoid the Latest Cyber Fraud Scheme
The “Pig Butchering Scam,” as it is popularly called, used to be a primitive swindle, but in recent times it has become an advanced form of forgery. The scam takes advantage of victims’ trust and...
EvilGynx Hack is a Threat to Small Businesses
In the current digital age, one familiar term small businesses should take note of and guard against is “evilgynx”. With evilgynx as a keyword, small businesses are able to understand the internet...
Dell OptiPlex computers no longer support legacy boot BIOS
In the realm of computer hardware, evolution is constant. Dell, a renowned name in the industry, has been at the forefront of innovation, consistently pushing boundaries to enhance user experience...
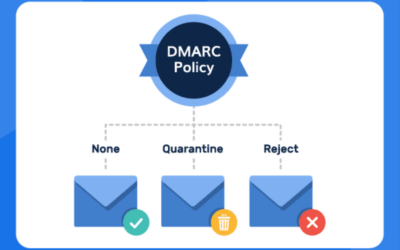
Understanding DMARC: Why It’s Essential for Email Security
In today's interconnected digital landscape, email remains a cornerstone of communication for businesses, organizations, and individuals alike. However, with the convenience and ubiquity of email...
Combatting the Rise of Check Fraud: The Imperative of Positive Pay
In an era dominated by digital transactions and online banking, it's easy to assume that traditional forms of payment, such as checks, have become obsolete. However, the reality is quite the...
MJN helps CPA firms become more modern and efficient in their billing practices
In the ever-evolving realm of financial technology, the adoption of seamless and automated solutions is crucial for businesses to stay competitive. Our IT firm takes pride in spearheading the...
SpamCop is blocking Microsoft IP addresses.
In today's digital age, email communication is a cornerstone of business operations. Companies rely on email services like Microsoft Office 365 to facilitate seamless communication, collaboration,...
Cyber Security
Cyber Security is a broad term that encompasses a number of different technologies, tools and practices that help the owners of computers and IT systems to protect them from cyber attacks. It can include password protection, firewalls to turn off access to the internet, anti-virus software and more. Though many companies use a variety of different technologies to protect against hackers, they all serve the same purpose, which is to keep data safe from intrusion by unauthorized people.
Learn more about this important topic and how to keep your business safe in our news articles about all things cyber security.
How a Managed Service Provider Can Help Your Business
Businesses rely on their computers and other devices to stay in touch with customers, run their operations and remain competitive. But the technology needed to do this has become increasingly...
Cloud Computing
Cloud computing is a great way for businesses to protect their data and IT systems without the high costs of in-house IT teams or dedicated servers. Instead of relying on one computer, cloud computing allows your business to have instant access to your files from any location using the internet. All cloud computing services are hosted by a third party and require a subscription, but this means you will never have to worry about losing important data due to hardware failure or human error.
How can your business best use cloud computing to improve its data security and business operations? We answer this and much more in our articles about all things cloud computing.
The Benefits of Cloud Computing for Your Business
Cloud computing is a relatively new concept. While it's becoming more popular, there are still many businesses that don't understand what cloud computing is or how it can benefit their operations....